Secure Internet Model 438379511 for Businesses

The Secure Internet Model 438379511 presents a structured approach to bolstering cybersecurity for businesses. It integrates advanced protocols aimed at safeguarding sensitive data and enhancing trust in online transactions. By addressing vulnerabilities and enabling operational efficiencies, this model serves as a vital tool for modern enterprises. However, the implementation process requires careful consideration of its essential components and strategies for successful integration. What implications does this have for businesses looking to thrive in an increasingly digital world?
Understanding the Secure Internet Model 438379511
The Secure Internet Model represents a structured framework designed to enhance cybersecurity for businesses operating in an increasingly digital landscape.
It establishes a secure network through rigorous implementation of internet protocols that govern data transmission. By prioritizing encryption, access controls, and monitoring, this model mitigates vulnerabilities, ensuring that businesses can operate freely while maintaining robust defenses against cyber threats.
Ultimately, it fosters trust in digital interactions.
Key Benefits for Businesses Implementing This Model
While businesses increasingly rely on digital platforms for operations, implementing the Secure Internet Model offers numerous advantages that significantly enhance their cybersecurity posture.
This model enables cost savings through streamlined operations and reduced overhead.
Furthermore, it promotes risk reduction by establishing robust protective measures against cyber threats, thereby fostering a secure environment that allows businesses to focus on growth and innovation without compromising their digital integrity.
Essential Components of the Secure Internet Model
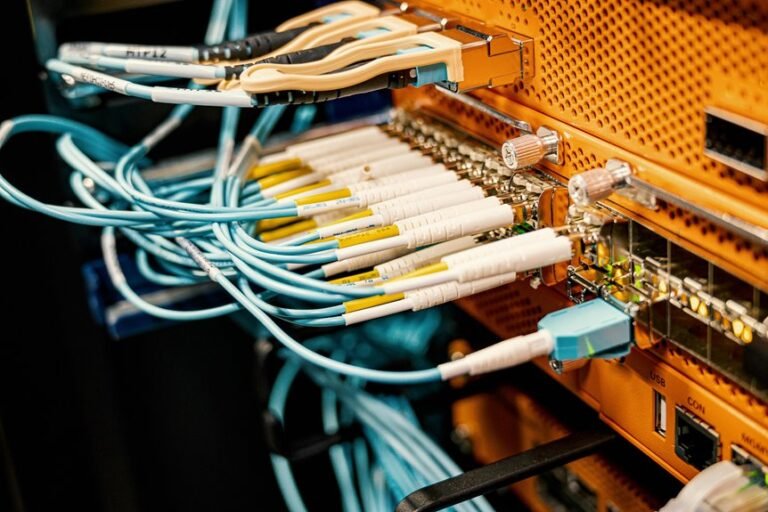
To establish a robust framework for cybersecurity, several essential components must be integrated into the Secure Internet Model.
Primarily, data encryption safeguards sensitive information during transmission, ensuring confidentiality.
Additionally, network security mechanisms, such as firewalls and intrusion detection systems, prevent unauthorized access and mitigate potential threats.
Together, these elements create a resilient infrastructure, empowering businesses to operate freely while maintaining stringent cybersecurity standards.
How to Successfully Integrate the Model Into Your Operations?
Integrating the Secure Internet Model into business operations requires a systematic approach that aligns cybersecurity strategies with organizational objectives.
Effective integration strategies must address potential operational challenges, such as resistance to change and resource allocation.
Prioritizing stakeholder engagement and continuous training is essential to foster a culture of security.
Ultimately, a cohesive implementation can enhance resilience while preserving the freedom of operational autonomy.
Conclusion
In conclusion, the Secure Internet Model 438379511 offers businesses a sophisticated safeguard against the ever-evolving landscape of cyber threats. By embracing this model, organizations not only shield their sensitive information but also embark on a transformative journey towards enhanced operational efficiency and innovation. The strategic integration of robust protocols fosters a resilient cybersecurity framework, allowing businesses to navigate the digital realm with confidence. Ultimately, this model serves as a beacon of security and trust in an increasingly interconnected world.